Level Up Your Business: The Power of a Strong MSP Partnership
Your Managed Service Provider (MSP) is more than just tech support—they're the secret weapon that propels your business forward. Our clients know the importance of a reliable, efficient IT infrastructure. But did you know that building a rock-solid MSP partnership can take your business to the next level? Let's dive...
Read More
Understanding DMARC Regulations
Domain-based Message Authentication, Reporting and Conformance (DMARC) is an email authentication protocol specification initially defined in early 2012. Twelve years later, DMARC remains a powerful tool to help businesses defend against threats posed by phishing attacks and emails scams. In 2024, new rules are fortifying the potency of DMARC’s protection...
Read More
The Rise of Ransomware: Why Every Business Needs a Cybersecurity Plan
Imagine waking up to the chilling message: "Your files are encrypted. Pay now or lose them forever." This isn't a dystopian movie plot; it's the harsh reality of ransomware, a cyberattack that's rapidly becoming a top threat for businesses of all sizes. The Stats Paint a Grim Picture In 2023,...
Read More
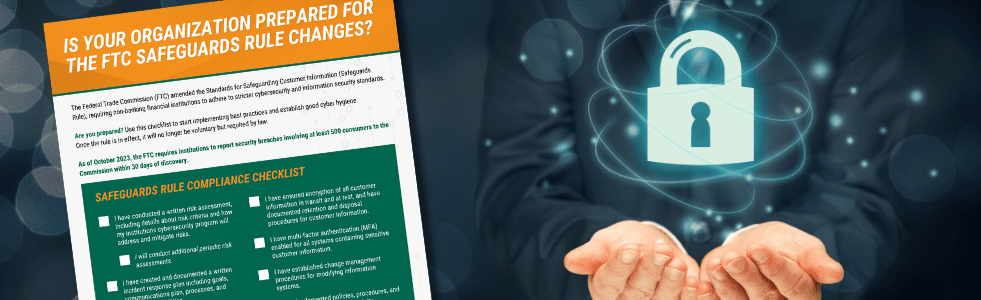
FTC Safeguards Rule 2024: Secure Your Data, Secure Your Business
Understanding the updated FTC Safeguards Rule for non-bank financial institutions If you’re a non-bank financial institution, you are probably already familiar with the FTC Safeguards rule put in place in October, 2021. However, you may not be familiar with one of the most recent updates to this rule. First, what...
Read More
Top 10 Cybersecurity Trends for 2024
The cybersecurity landscape is undergoing a seismic shift, driven by technological advancements, evolving threats, and a heightened focus on regulation. From the talent crunch in cybersecurity to the rise of Generative AI and the increasing importance of soft skills, the industry is bracing for a transformative year. This guide delves...
Read More
Don’t be a Statistic: Protect Your Manufacturing Business Against Cyberattacks by Establishing a Policy of Cyber Resilience
Last year, the United States faced a staggering financial toll of over $10 billion due to cyberattacks. Alarmingly, a considerable portion of these losses impacted the manufacturing sector, making it the second most targeted industry for cybersecurity threats. The concept of cyber resilience—preparing for, responding to, and recovering from cyber...
Read More
5 Essential Cybersecurity Tips for Small Business Owners
In the modern business landscape, reliance on technology by small business owners is increasing, fueling both growth and efficiency. Technology tools add many essential benefits but also introduce complex challenges with cybersecurity. A survey conducted by Connectwise in 2022 revealed a startling trend: 76% of small businesses had fallen victim...
Read More
Choosing the right IT support model for your business: in-house, outsourced, or co-managed
In today's technology-driven business landscape, having reliable and efficient IT support is crucial for smooth operations and growth. Choosing the optimal IT support model is critical for businesses facing increasingly diverse technology challenges. This blog explores the benefits of three primary IT support models - in-house, outsourced, and co-managed -...
Read More